Has moved beforehand e-wallets in terms of extent and the cost of digital transactions, mainly because of the system’s simplicity. However, this simplicity of UPI transactions seemingly assists fraudsters in conning those who won’t take note of details. Recently, a Twitter user, @mohmaaya, shared her enjoyment of ways a fraudster attempted to entice her by sending her a request to pay up while she turned into trying to sell something online. She might have misplaced a large quantity if she had no longer paid attention. Mint spoke to payment businesses to understand the mechanism utilized by fraudsters. But first, allow us to know how UPI works and how it’s open to the possibility of fraud.
How UPI works
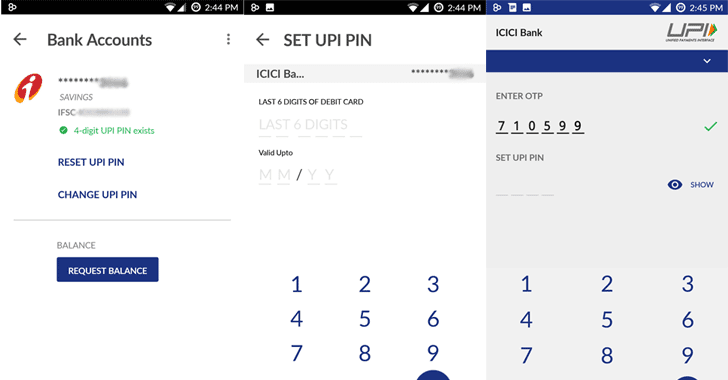
To transfer or receive money using UPI, you want to have activated UPI for your financial institution account. To do that, you want to have a cellular phone connection related to the financial institution account. When you enable UPI, you also want to create a VPA (digital fee cope with), like a UPI ID.
Some UPI apps also assist you in testing if a wide variety of your contact e-books is lively on the platform. To complete a VPA transaction, both the sender and the receiver want to be active on UPI. If you’re the sender, you’ll need to enter VPA or pick out a contact from inside the app, which activates you to input the amount to be sent. After clicking “pay”, you want to enter your UPI PIN to complete the transaction.
For industrial transactions, you want to pay for a buy; like a web purchase, you want to post your VPA to the service provider online. The service provider then sends you an “acquire request, ” which is time-sure. You must log into your UPI app and approve or decline the request. If you pick out to approve the transaction, you need to enter your UPI PIN. But even for a man or woman-to-man transactions, you can ship a request to accumulate money from someone else, as the fraudster did with @mohmaaya. This function is being misused with the aid of cheats.
